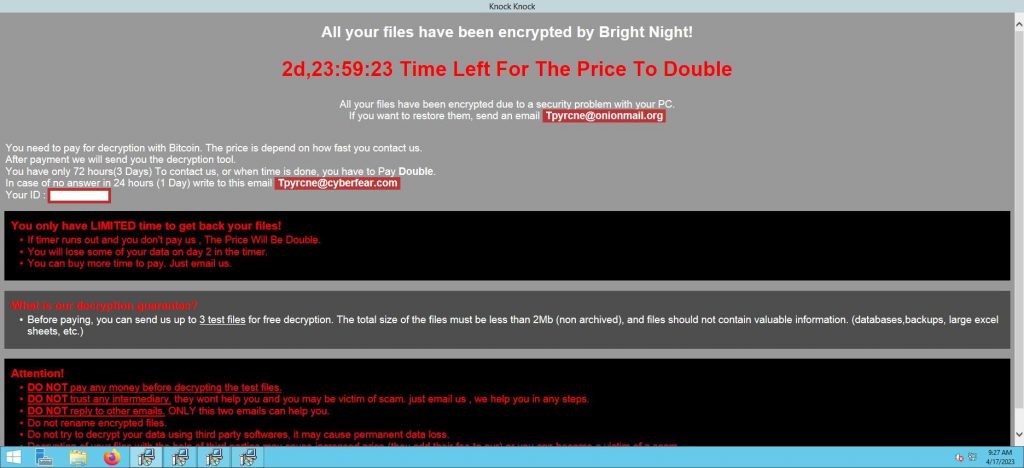
We would like to inform you that at least one of our Deception Devices has detected a new Bright Night Ransomware wave variant recently.
As of today this #malware variant can be distributed completely undetected by traditional #antivirus running in organizations and corporations. When the payload is executed in an endpoint, local and network share files will become immediately encrypted. This means the files won’t be accessible anymore.
Why do we think is especially dangerous?
The MD5 Hash/SHA1 signature of the payload suggests that instead of being a CryptoLocker Ransomware application, the ‘File is Distributed by Microsoft’ completely trusted and operating as a system process running undetected by any antivirus out there.
You can check the #VirusTotal results following this link
It is likely the MD5 Hash / SHA1 signature to have been counterfeited or spoofed (collision attack) and this is why this Zero-Malware can have potentially catastrophic results for victims out there.
We’d love to hear from Malware Researchers and Ransomware teams fighting this type of attacks. One of our #DeceptionStrike devices detected this attack last night and we have gathered a lot of Threat Intelligence around it ( entry vector, payload, source IP addresses of the attacker etc..).
The possibility to reverse engineer the process identifying the encryption key used is real; if you or your team have experience around this, let us know!
On the contrary, if you are a victim of this new Ransomware variant do not pay the ransom, we might be able to help you.
Visit and bookmark this link https://lnkd.in/ewf6wTjc as further analysis will be conducted and shared and I hope we can help.
Very, very nasty stuff is happening out there, if you are Information Security Professionals do yourselves a favor and check whether last night-backup is healthy or not !
Stay safe, stay informed!
#deceptiontechnology #ransomware #cyberdeception #infosec #threathunting #cybersecurity #pentesting #blockchain #cryptolocker #malware #malwareresearch #threatintelligence #devsecops #reverseengineering #informationtechnology #business #investors #vc #crowdfunding #startups #Network #NetworkSecurity #endpointsecurity #redteam #technology #DataSecurity #windows #DFIR #ethicalhacking #MDR #DetectionRespoonse #crowdstrike #cylance #paloaltonetworks #sentinelone #trustlook