honeypot vs honeynet
What is a Honeypot
A honeypot is a security mechanism that creates a virtual trap to lure attackers. An intentionally compromised computer system allows attackers to exploit vulnerabilities so you can study them to improve your security policies. You can apply a honeypot to any computing resource from software and networks to file servers and routers.
Honeypots are a type of deception technology that allows you to understand attacker behavior patterns. Security teams can use honeypots to investigate cybersecurity breaches to collect intel on how cybercriminals operate. They also reduce the risk of false positives, when compared to traditional cybersecurity measures, because they are unlikely to attract legitimate activity.
Honeypots vary based on design and deployment models, but they are all decoys intended to look like legitimate, vulnerable systems to attract cybercriminals.
Honeynet: A Network of Honeypots
A honeynet is a decoy network that contains one or more honeypots. It looks like a real network and contains multiple systems but is hosted on one or only a few servers, each representing one environment. For example, a Windows honeypot machine, a Mac honeypot machine and a Linux honeypot machine.
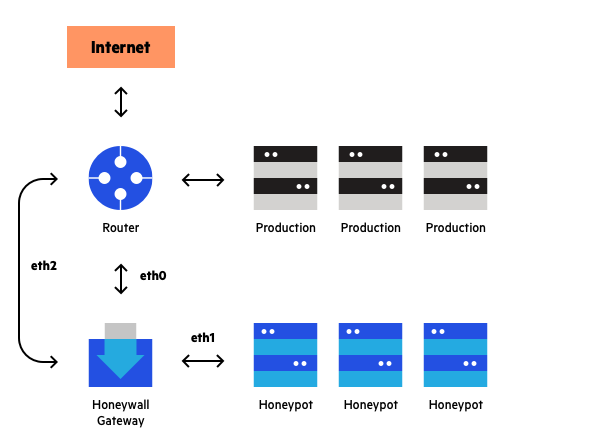
A “honeywall” monitors the traffic going in and out of the network and directs it to the honeypot instances. You can inject vulnerabilities into a honeynet to make it easy for an attacker to access the trap.
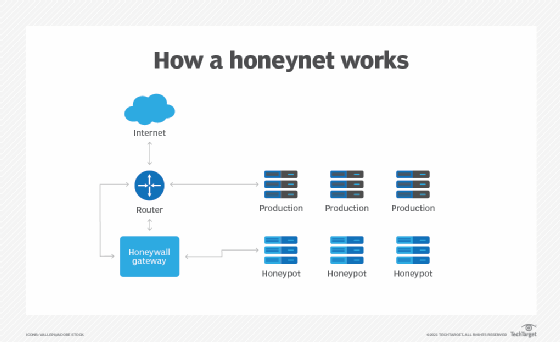
Example of a honeynet topology
Any system on the honeynet may serve as a point of entry for attackers. The honeynet gathers intelligence on the attackers and diverts them from the real network. The advantage of a honeynet over a simple honeypot is that it feels more like a real network, and has a larger catchment area.
This makes honeynet a better solution for large, complex networks – it presents attackers with an alternative corporate network which can represent an attractive alternative to the real one.
Get your intel directly from the experts.
We are sharing all the latest and greatest cybersecurity knowledge in our webcasts, events, demos and more–come join us.
Overview of deception technology
Whether you want to picture deception technology as a worm dangling on a fish hook, a chunk of cheddar hidden in a mousetrap, or the notes of an enticing siren song luring sailors to their death, the message is the same: Deception technology is bait. By setting irresistible traps that appear to be legitimate IT assets, it entices attackers on your internal network to interact with them, triggering an alert and giving your team the time, insight, and context they need to respond effectively. Because no one within your organization needs to interact with deception technology as part of their job, any activity it records is automatically suspicious. Therefore, a key benefit of deception technology is high-fidelity alerts that identify very specific malicious behaviors.
Deception technology can reduce attacker dwell time on your network, speed up mean time to detect and remediate, reduce alert fatigue, and provide vital information around indicators of compromise (IOCs) and tactics, techniques, and procedures (TTPs).
Honey users
Honeypots are decoy systems or servers that are deployed alongside production systems within your network. They can look like any other machine on the network or be deployed to look like something an attacker could target. There are many applications and use cases for honeypots, as they work to divert malicious traffic away from important systems, identify anomalous network scans, and reveal information about attackers and their methods.
In terms of objectives, there are two types of honeypots. Research honeypots gather information about attacks and are used specifically for studying malicious behavior out in the wild. Looking at both your environment and the wider world, they gather information on attacker trends, malware strains, and vulnerabilities that are actively being targeted by adversaries. This can inform your preventive defenses, patch prioritization, and future investments.
Production honeypots, deployed on your network, help reveal internal compromise across your environment and gives your team more time to respond. Information gathering is still a priority, as honeypots give you additional monitoring opportunities and fill in common detection gaps around identifying network scans and lateral movement.
Straightforward and low-maintenance, honeypots help you break an attack chain and slow adversaries down with high-fidelity alerts and contextual information. Interested in learning more about honeypots? Check out our page on honeypot technology.

